
نمونه سوالات آزمون
Implementing Cisco IP Routing - exam 300-101
Topic 6, Infrastructure Services
QUESTION NO: 81
Refer to the exhibit.
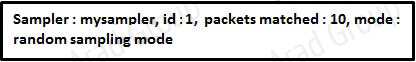 Which statement about the output of the show flow-sampler command is true?
Which statement about the output of the show flow-sampler command is true?
A. The sampler matched 10 packets, each packet randomly chosen from every group of 100 packets.
B. The sampler matched 10 packets, one packet every 100 packets.
C. The sampler matched 10 packets, each one randomly chosen from every 100-second interval.
D. The sampler matched 10 packets, one packet every 100 seconds.
Answer: A
Explanation:
The sampling mode determines the algorithm that selects a subset of traffic for NetFlow processing. In the random sampling mode that Random Sampled NetFlow uses, incoming packets are randomly selected so that one out of each n sequential packets is selected on average for NetFlow processing. For example, if you set the sampling rate to 1 out of 100 packets, then NetFlow might sample the 5th, 120th, 199th, 302nd, and so on packets. This sample configuration provides NetFlow data on 1 percent of total traffic. The n value is a parameter from 1 to 65535 packets that you can configure.
QUESTION NO: 82
What is the result of the command ip flow-export destination 10.10.10.1 5858?
A. It configures the router to export cache flow information to IP 10.10.10.1 on port UDP/5858.
B. It configures the router to export cache flow information about flows with destination IP 10.10.10.1 and port UDP/5858.
C. It configures the router to receive cache flow information from IP 10.10.10.1 on port UDP/5858.
D. It configures the router to receive cache flow information about flows with destination IP 10.10.10.1 and port UDP/5858.
Answer: A
Explanation:
To enable the exporting of information in NetFlow cache entries, use the ip flow-export destination command in global configuration mode.
Syntax Description
ip-address
IP address of the workstation to which you want to send the NetFlow information.
udp-port
UDP protocol-specific port number.
QUESTION NO: 83
Which type of traffic does DHCP snooping drop?
A. discover messages
B. DHCP messages where the source MAC and client MAC do not match
C. traffic from a trusted DHCP server to client
D. DHCP messages where the destination MAC and client MAC do not match
Answer: B
QUESTION NO: 84
Which two commands would be used to troubleshoot high memory usage for a process? (Choose two.)
A. router#show memory allocating-process table
B. router#show memory summary
C. router#show memory dead
D. router#show memory events
E. router#show memory processor statistics
Answer: A,B
QUESTION NO: 85
The following configuration is applied to a router at a branch site:
ipv6 dhcp pool dhcp-pool
dns-server 2001:DB8:1:B::1
dns-server 2001:DB8:3:307C::42
domain-name example.com
!
If IPv6 is configured with default settings on all interfaces on the router, which two dynamic IPv6 addressing mechanisms could you use on end hosts to provide end-to-end connectivity? (Choose two.)
A. EUI-64
B. SLAAC
C. DHCPv6
D. BOOTP
Answer: A,B
QUESTION NO: 86
The enterprise network WAN link has been receiving several denial of service attacks from both IPv4 and IPv6 sources. Which three elements can you use to identify an IPv6 packet via its header, in order to filter future attacks? (Choose three.)
A. Traffic Class
B. Source address
C. Flow Label
D. Hop Limit
E. Destination Address
F. Fragment Offset
Answer: A,C,D
QUESTION NO: 87
A network engineer has set up VRF-Lite on two routers where all the interfaces are in the same VRF. At a later time, a new loopback is added to Router 1, but it cannot ping any of the existing interfaces. Which two configurations enable the local or remote router to ping the loopback from any existing interface? (Choose two.)
A. adding a static route for the VRF that points to the global route table
B. adding the loopback to the VRF
C. adding dynamic routing between the two routers and advertising the loopback
D. adding the IP address of the loopback to the export route targets for the VRF
E. adding a static route for the VRF that points to the loopback interface
F. adding all interfaces to the global and VRF routing tables
Answer: A,B
QUESTION NO: 88
Refer to the exhibit. The network setup is running the RIP routing protocol. Which two events will occur following link failure between R2 and R3? (Choose two.)
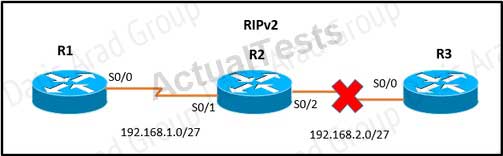 A. R2 will advertise network 192.168.2.0/27 with a hop count of 16 to R1.
A. R2 will advertise network 192.168.2.0/27 with a hop count of 16 to R1.
B. R2 will not send any advertisements and will remove route 192.168.2.0/27 from its routing table.
C. R1 will reply to R2 with the advertisement for network 192.168.2.0/27 with a hop count of 16.
D. After communication fails and after the hold-down timer expires, R1 will remove the 192.168.2.0/27 route from its routing table.
E. R3 will not accept any further updates from R2, due to the split-horizon loop prevention mechanism.
Answer: A,C
QUESTION NO: 89
Which three benefits does the Cisco Easy Virtual Network provide to an enterprise network? (Choose three.)
A. simplified Layer 3 network virtualization
B. improved shared services support
C. enhanced management, troubleshooting, and usability
D. reduced configuration and deployment time for dot1q trunking
E. increased network performance and throughput
F. decreased BGP neighbor configurations
Answer: A,B,C
QUESTION NO: 90
Refer to the exhibit. Which statement is true?
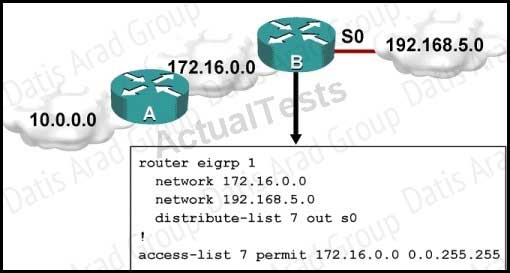
A. Traffic from the 172.16.0.0/16 network will be blocked by the ACL.
B. The 10.0.0.0/8 network will not be advertised by Router B because the network statement for the 10.0.0.0/8 network is missing from Router B.
C. The 10.0.0.0/8 network will not be in the routing table on Router B.
D. Users on the 10.0.0.0/8 network can successfully ping users on the 192.168.5.0/24 network, but users on the 192.168.5.0/24 cannot successfully ping users on the 10.0.0.0/8 network.
E. Router B will not advertise the 10.0.0.0/8 network because it is blocked by the ACL.
Answer: E
QUESTION NO: 91
Which technology was originally developed for routers to handle fragmentation in the path between end points?
A. PMTUD
B. MSS
C. windowing
D. TCP
E. global synchronization
Answer: A
QUESTION NO: 92
Which traffic characteristic is the reason that UDP traffic that carries voice and video is assigned to the queue only on a link that is at least 768 kbps?
A. typically is not fragmented
B. typically is fragmented
C. causes windowing
D. causes excessive delays for video traffic
Answer: A
QUESTION NO: 93
A network administrator is troubleshooting a DMVPN setup between the hub and the spoke. Which action should the administrator take before troubleshooting the IPsec configuration?
A. Verify the GRE tunnels.
B. Verify ISAKMP.
C. Verify NHRP.
D. Verify crypto maps.
Answer: A
QUESTION NO: 94
To configure SNMPv3 implementation, a network engineer is using the AuthNoPriv security level. What effect does this action have on the SNMP messages?
A. They become unauthenticated and unencrypted.
B. They become authenticated and unencrypted.
C. They become authenticated and encrypted.
D. They become unauthenticated and encrypted.
Answer: B
QUESTION NO: 95
A network engineer is investigating the cause of a service disruption on a network segment and executes the debug condition interface fastethernet f0/0 command. In which situation is the debugging output generated?
A. when packets on the interface are received and the interface is operational
B. when packets on the interface are received and logging buffered is enabled
C. when packets on the interface are received and forwarded to a configured syslog server
D. when packets on the interface are received and the interface is shut down
Answer: A
QUESTION NO: 96
Refer to the exhibit. The command is executed while configuring a point-to-multipoint Frame Relay interface. Which type of IPv6 address is portrayed in the exhibit?
![]() A. link-local
A. link-local
B. site-local
C. global
D. multicast
Answer: A
QUESTION NO: 97
An engineer executes the ip flow ingress command in interface configuration mode. What is the result of this action?
A. It enables the collection of IP flow samples arriving to the interface.
B. It enables the collection of IP flow samples leaving the interface.
C. It enables IP flow while disabling IP CEF on the interface.
D. It enables IP flow collection on the physical interface and its subinterfaces.
Answer: A
QUESTION NO: 98
What is the primary service that is provided when you implement Cisco Easy Virtual Network?
A. It requires and enhances the use of VRF-Lite.
B. It reduces the need for common services separation.
C. It allows for traffic separation and improved network efficiency.
D. It introduces multi-VRF and label-prone network segmentation.
Answer: C
QUESTION NO: 99
How does an IOS router process a packet that should be switched by Cisco Express Forwarding without an FIB entry?
A. by forwarding the packet
B. by dropping the packet
C. by creating a new FIB entry for the packet
D. by looking in the routing table for an alternate FIB entry
Answer: B
QUESTION NO: 100
Which statement about dual stack is true?
A. Dual stack translates IPv6 addresses to IPv4 addresses.
B. Dual stack means that devices are able to run IPv4 and IPv6 in parallel.
C. Dual stack translates IPv4 addresses to IPv6 addresses.
D. Dual stack changes the IP addresses on hosts from IPv4 to IPv6 automatically.
Answer: B